Online shopping safety
The Internet privacy problem
When you are shopping, banking or accessing other sensitive or confidential
information online, how can you be sure that no one can monitor or intercept this
personal information? Moreover, how can you be sure that someone can’t get
this information from your computer later?
The answer of the first question is simpler that the second one. Mil Shield is a
powerful privacy protection tool that can automatically clean all online and offline
traces from your computer, which is very important to your Internet privacy, as
you will see below.
|
|
|
|
|

4.34 MB - 5 sec with broadband
|
|
|
|
|
|
Secure pages and secure connections
Everything that you enter in the online forms when you are shopping, travels through
many (tens or even hundreds) switching devices and computers. In order to be sure
that no one can intercept this information, a special way of communication is used,
called Secure Socket Layer (SSL). SSL ciphers (encrypts) the information on your
computer and deciphers (decrypts) the information on the Web server that you are
accessing. But how can you be sure that SSL is used when you are shopping online?
First, you have to look at the address bar of your browser and see what the address
of the page where you enter your personal and credit card information looks like. If the
address begins with https: (s for secure) instead of
http:, then this page is using SSL. Note that only the page(s) where
you actually enter your personal and credit card information need to be protected with
SSL. All other pages on the Web site in most cases don’t use SSL because they don’t need to.
If you are using Internet Explorer you can use more comfortable indicators for the level of security of the site.
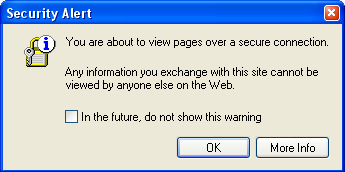
- When you are about to open security protected page, you may get the message
window shown below. If you don’t see the message, it may have been turned off
(click here to learn how to switch this message on). A similar message pops up when
you leave the security protected page and enter ordinary Web page.
To turn off this warning, click to check In the future, do not show this
warning before you click OK.
 |
- If the Security Alert is not showing up,
you can turn it back on. On the Internet Explorer Tools menu, choose
Options. On the Advanced Tab, scroll to the very bottom of
the list. Under Security options category, click to check
Warn if changing between secure and not secure mode, and then click
OK. From then on, you will see an alert message every time you enter (or leave) a
secure page.
- Once you get to the site, the Web address begins with https:
("s" for secure), and the locked padlock at the bottom of the window
confirms the site has increased security. You can rest your mouse pointer on the
lock to see the level of encryption.
Digital certificates, cipher strength and Internet privacy
With SSL (the secure protocol described above) you can be sure that no one can
intercept and decode the private information sent to the online store or whatever
web page you are accessing via secure connection. However, there is another danger –
how can you be sure that the online shop itself is not a cheat or impostor?
To address this concern, when you visit the online store order page and you submit
your personal data, the online store server automatically sends its digital certificate.
This is essentially an electronic ID card that proves the online store identity to your
browser, and verifies that it was issued by a certificate authority that your browser
trusts. This certificate is issued to the online store by a trusted third party called a
certificate authority. In addition to proving the online store identity, the
certificate provides a cryptographic "key" (cipher) that is used to encode and
decode your communication with the online store. Once your browser approves the
certificate, the secure server encrypts any information before it travels across the Internet.
The information you send via secure connection is protected using encryption, a method of
scrambling data that helps to prevent unauthorized users from reading or tampering with it.
When your computer and the site—say, your bank—are about to exchange encrypted data,
a connection called a handshake is established between the two. The bank's server
transmits the bank's key to your computer. Your computer then encrypts a unique key for
that session, and for the rest of the transaction, your personal information is encrypted
and authenticated using keys derived from this exchange. So if someone captures
your information, it will appear as garbled text without the secret key. Once your data
has been transmitted, it is decoded back into its original form, using a similar key.
This may seem complicated but everything is handled by your browser in a matter of
seconds so you don’t have to worry about the details of the process.
Each digital certificate has validity period. It this period is over or certificate is not
valid for some other reason then the browser will notify you. With Internet Explorer the
little padlock in the bottom of the browser window will not be locked and you can
double-click on the padlock icon in order to see what is wrong. Some secure Web
pages place an image on the bottom of the page that leads to their digital certificate.
You can click on this image to see the details of the security certificate directly from
the certificate authority Web site.
The cipher strength is measured in the number of bits supported by your browser. It
translates to how long and complicated (and thus hard-to-crack) the key code used
to encrypt your data is. The current standard for secure connections is 128-bit.
(A bit is the smallest unit of data in a computer.) It is supported by most
popular browsers.
NOTE: Do not confuse 128-bit encryption with a 32-bit or 64-bit processor,
which refers to the number of bits that a computer can process at a time and does
not affect the cipher strength, which is determined only by the capabilities of your browser.
TIP: If you are using Internet Explorer, you can find out the cipher
strength of current secure connection if you rest your mouse over the padlock icon
in the bottom of the browser window. If you want to find out which is the maximum
cipher strength, supported by Internet Explorer, click on Help menu and then select
About Internet Explorer. The cipher strength is listed in the dialog window
just below the version of Internet Explorer.
Traces left on your computer
The discussion above covers the protection of your Internet privacy from Internet cheats
or impostors. However the encryption can not help if someone gets to control your PC or has
access to your computer through one of the numerous security holes in the
operating system and application software. The thing is that Internet Explorer leaves many traces of your
Web surfing. These include Internet history,
cookies,
Temporary Internet files (a.k.a.
Internet cache) and AutoComplete forms and passwords. If an intruder gets access to
these traces, he can have a full record of all Web surfing and even some of your
computer activities that are not related to Internet.
You can delete some of these traces through Internet Explorer options but not all of
them are really deleted (see the article Delete Index.dat files for the most obscure and
hard to erase traces). Furthermore, it is real pain to have to clean even these traces because there is
no centralized place to control this and there is no way
to automate the process. Finally, some of the traces are actually good for your browsing
experience – Internet cache speeds up the browsing, cookies protect you from
entering your user information over and over again and history makes it easy
to type the addresses of your favorite Web sites.
Mil Shield is a powerful privacy protection program that was designed specifically to clean
and shred all online and offline traces. Using this tool you can clean all traces with
one click of the mouse or even better – you can set automatic cleaning of the
traces each time when you turn on or turn off your computer or when you close
all your Internet Explorer windows. Another benefit is the ability to preserve the tracks
from some chosen by you sites (selective cleaning), which makes your browsing faster,
more comfortable and safe.
Mil Shield also cleans all other tracks as cookies, history, cache, AutoComplete
records, UserData records, history of recently used folders and
documents and many other tracks as well as tracks of many popular applications.
Conclusion
As we saw the online shopping experience can be safe and joyful only if we take
some precautions. Here is a summary of the steps that you need to follow in
order to protect your Internet privacy:
- Check if the order page(s) are SSL protected. The address of the page must
begin with https: and (if you are using Internet Explorer) the little
padlock icon on the bottom of the browser window must be locked.
- If the security alerts of Internet Explorer don’t bother you, leave them
turned on (or turn them on if they are turned off).
- Use a browser that supports 128-bit cipher strength and (if you are
really paranoid) check the digital certificates of the secure pages.
- Use a privacy protection program like Mil Shield in order to avoid the
possibility of someone that can steal your personal information after the online
transaction.
Well, happy shopping!
| 
